Archive for the ‘online backup’ tag
It’s 2016 – Is Your Office Server or Web Site Being Held Hostage? no comments
 The latest wave of computer security news may sound like the headline of a new Bruce Willis movie – but Ransomware is now part of the daily conversation between not only security experts, but unfortunately by office managers and PC users across the globe having to deal with the ramifications.
The latest wave of computer security news may sound like the headline of a new Bruce Willis movie – but Ransomware is now part of the daily conversation between not only security experts, but unfortunately by office managers and PC users across the globe having to deal with the ramifications.
This year malware infections, more specifically ransomware, have seen an exponential growth. They are also becoming more sophisticated, using newer methods that are not only harder to detect, but also require less user interaction.
Security researchers report attackers are not only upgrading their malware to make it more unbreakable, they are also using unique methods of distribution. In some cases, these methods require no user interaction at all.
In the past, most ransomware infections occurred via phishing attacks, which required a user to click on a malicious website or email link. But these newer attacks are less dependent on user interaction and more dependent on unpatched vulnerabilities or poor security practices.
These new breeds of ransomware are utilizing more advanced methods to attack computers and encrypt their files, before you even realize what’s happened. You are then forced to either pay the ransom or hope you have a backup recent enough to prevent any lost data.
To protect yourself you need to follow best practices, such as
- backup your servers and PC’s
- backup your servers and PC’s
- see item (1) and (2) above (seriously!)
- keep your software and systems patched and up-to-date
- Have a corporate gateway firewall with advanced threat protection
- Have / Install / Update local AntiVirus and Malware Software protection
- Always avoid opening un-expected emails or attachments
- Avoid clicking to web sites you don’t recognize (especially if sent in email)
- if you aren’t backing up your servers and PC’s already – stop reading and visit https://turnkeyvault.com/
It’s pretty simple – the same things that protect your office data and servers from most threats apply here, but the damage of ransomware encrypting and disabling all your corporate data within seconds or minutes is real and has lead to some high profile cases including hospitals being locked out of all their data due to ransomware! Don’t let your business fall victim to the bad-named villain of a Bruce Willis movie – ransomware is among the most costly cyber threats actively attacking businesses right this very second.
Make no mistake – backing up your data is a must have in any security policy, and utilizing a secure remote cloud based backup solution such as TurnKey Vault is ideal. Make sure whatever backup solution you deploy offers data encryption, supports both desktop PC’s and Macs, as well as Linux and Windows based servers. A backup solution like TurnKey Vault offers live cloud replication which will get you back on your feet in minutes in case of a true disaster by creating a live cloud-based copy of any PC workstation or Server accessible from anywhere over the Internet to get you access to your data and applications quickly. If ransomware takes over your office network you can spin up a backup live copy of your servers and PC’s with TurnKey Vault from a time before the ransomware took over your office – and will have you saying “Yippee Ki-Yay” just like Bruce Willis as the ransomeware data hostage takers wont ever see a dime, and you will have all your data safe and secure.
Follow Us :
Share :
DROWN Attacks – Web Encryption No Longer Safe – Is My Web Site at Risk? no comments
 Encryption fills the headlines with stories of APPLE and decoding iPhones – but with all the security challenges and cyber threats today – its getting hard pressed to have a web site, computer, or mobile device and not realize your data is as private as you once thought. Encryption is what protects (hides) the details of what we do online certain web sites – keeping your private banking or purchasing data (or online traffic hidden) from prying eyes. But last month a new threat called DROWN was publicized that essentially made it so many web sites you shop, visit or utilize that you thought were secure and private via their https SSL encrypted access turned out to not be so private.
Encryption fills the headlines with stories of APPLE and decoding iPhones – but with all the security challenges and cyber threats today – its getting hard pressed to have a web site, computer, or mobile device and not realize your data is as private as you once thought. Encryption is what protects (hides) the details of what we do online certain web sites – keeping your private banking or purchasing data (or online traffic hidden) from prying eyes. But last month a new threat called DROWN was publicized that essentially made it so many web sites you shop, visit or utilize that you thought were secure and private via their https SSL encrypted access turned out to not be so private.
DROWN, standing for Decrypting RSA with Obsolete and Weakened eNcryption, is an xample of a cross-protocol attack that exploits weaknesses in the widely used online encryption protocol, SSLv2. Using weaknesses in the SSLv2 implementations against TLS (transport layer security) hackers can “decrypt passively collected TLS sessions from up to date clients.” Or in simpler terms, hackers and anyone can see what you are doing, your personal details, and more when you thought you may of been protected by that SSL ‘lock’ protected symbol next to the web site you were shopping or visiting.
TLS is probably the most important security protocol on the internet. Almost every action you take on the internet relies on the use of a TLS version. Not just you accessing a web site, but a lot of the back behind the scenes things like email transmission, to database connections, to sending files between servers for backups.
Fortunately, the latest versions of OpenSSL do not utilize SSLv2 connections by default. However, if your certificate or key is being used in another location on a server that supports SSLv2, you could be at risk. For example, the mail service (POP, IMAP, SMTP connections).
A DRWON attack would be able to decrypt HTTPS connections, sending specifically designed packets to another server. If the certificate is on more than one server, it is possible a MitM (man in the middle) attack can be successful.
Isn’t SSLv2 depreciated? Why is this still a threat? In the early 2000’s SSLv2 was still supported by browsers, to be used as a fallback protocol. An attacker could easily trick the browser into using an older protocol. Thankfully, this is no longer an issue if you are using a recent version of your web browser.
While browsers are no longer supporting SSLv2, most servers still do. Most servers are configured to use both TLS and SSLv2. This means both protocols would use the same RSA private key. Therefore, any bugs in the SSLv2 protocol that use the private key, potentially could affect the security of TLS.
While this all may sound a little scary, as most security vulnerabilities are. TurnKey Internet takes all security avenues very seriously. Our web hosting servers and software are always kept up to date. If your account is on any of our shared hosting packages, you have nothing to worry about. Just in case, you want to test your sites security against DROWN or the server your account is hosted on. Please feel free to do so here – https://drownattack.com/#check You will need to use the IP address your site is living on and not your domain name – which you can easily find by using a DNS lookup service such as http://www.getip.com/.
If you need assistance finding your web sites IP, or reviewing your security please send us a support ticket (helpdesk@turnkeyinternet.net) and we would be happy to tell you.
Follow Us :
Share :
TurnKey Internet, Inc Launches Cloud Backup with Business Continuity Service no comments
TurnKey Internet, Inc Launches Cloud Backup with Business Continuity Service
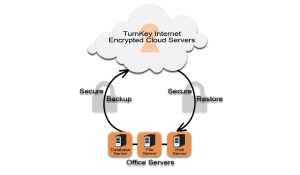
 LATHAM, NEW YORK (September 22nd, 2015) – Sustainable IT solutions provider TurnKey Internet, Inc. announced today the launch of their TurnKey Vault Secure Cloud Backup service. The all new product delivers next-generation online backup services focused on business continuity and disaster recovery (BCDR) to individuals, businesses and large scale organizations across the globe.
LATHAM, NEW YORK (September 22nd, 2015) – Sustainable IT solutions provider TurnKey Internet, Inc. announced today the launch of their TurnKey Vault Secure Cloud Backup service. The all new product delivers next-generation online backup services focused on business continuity and disaster recovery (BCDR) to individuals, businesses and large scale organizations across the globe.
TurnKey Vault offers next-generation backup technology including bare metal recovery, Linux, Windows and Mac operating system support, encrypted data protection, as well as backups for enterprise databases such as Oracle, MSSQL and MySQL. TurnKey Vault fills the void that exists with typical online backup solutions, by offering true business continuity disaster recovery (BCDR) through next-generation Virtual Disaster Recovery combined with live cloud replication to provide instant recovery to businesses by restoring any server, PC, or laptop into a cloud-based virtual private server that is accessible via the Internet.
TurnKey Vault’s live cloud replication allows instant restoration of your operating system, files, configuration, registry files, software programs, licenses, and everything to bring your laptop, PC, or server back into full production without any additional hardware or IT staff. Your fully restored cloud-based server, PC or laptop is cloud-ready and accessible via the Internet via any mobile phone, tablet, PC using remote desktop protocols or any web browser to access your entire system.
”Data loss is a reality – you are more likely to lose your business data in the next 7 years than get audited by the IRS.” said Adam Wills, CEO of TurnKey Internet. He continued, “The reality of the current generation backup solutions out there is that it’s not enough to just backup your data and hope to put the pieces back together after disaster strikes- that can lead to countless days or weeks of lost business productivity and expensive IT support staff time. With our TurnKey Vault technology combined with our cloud-based datacenter services, we can literally restore an entire office building of lost servers and PCs back into fully accessible and functional copies so your business can get back up and running fast.”
TurnKey Vault offers a free for life 10 GB plan with all enterprise features enabled and a reseller system for VAR’s and channel partners to offer private label branded Secure Cloud Backup services to an unlimited number of clients or devices. For more information visit https://TurnKeyVault.com.
About Turnkey Internet
Founded in 1999, TurnKey Internet, Inc. is a full-service green data center and leading provider of sustainable web hosting and IT solutions. From its SSAE 16 Type 2 and ENERGY STAR® certified facility in Latham, NY—New York’s Tech Valley Region—TurnKey offers cloud-based hosted services, web hosting, communication services, web-based IT systems, software as a service (SaaS), enterprise colocation services, and computing as a service to clients in more than 150 countries. For more information, please call (518) 618-0999 or visit www.turnkeyinternet.net/media.
Follow Us :Share :
Advanced Cloud Backup for Servers, PCs, and your Office to achieve full Business Continuity no comments
 In the past, I’ve spoke to you about purchasing backup software. I’ve compared having backup software for your server like having car insurance. I’ve also spoken with you about the different type of backup technologies that exist. I went into details about a few different types of technologies. These were the following:
In the past, I’ve spoke to you about purchasing backup software. I’ve compared having backup software for your server like having car insurance. I’ve also spoken with you about the different type of backup technologies that exist. I went into details about a few different types of technologies. These were the following:
- Bare Metal backup/restores
- Cloud Backups
- Virtual Server backups
For more information, check it out at TurnkeyVault.com
You can read about these technologies on our blog here For this article, I will be talking about a new type of backup software. A brand new product that I’m very excited to announce that combines many of the different backup technologies and creates a new, hybrid backup system. A system that allows you to ensure business continuity for your customers. For those of you who do not know what business continuity is, I shall explain. Business continuity means that your business goes on even if your systems fail. Restores are therefore fast and even if the system is down, continuity means you still have access to key piece of business data. Maintaining business continuity should be one of your main focuses as a business owner.
Our new backup product helps to ensure business continuity by combing the best of the backup technologies presently on the market. To do this, our software must have address the following needs
- Ability to create server backups and workstation backups
- Ability to create backups locally as well as to the cloud
- Ability to only backup files that have changed in a system
In order to show you the greatness of the new software, I will go through each ability listed above and show how these 3 key areas combine to provide you with unparalleled continuity for you business. Shall we begin?
Ability to create server backups and workstation backups
Server backups are the main component of any data protection installation. Servers are where all of the data resides. This includes current, recent and in many cases, older data. The server also is where operating systems, applications, configurations and system states reside. Ensuring these assets is the main job for any business owner or solution provider. Now while most business owners ensure that server backups exist, many over look their individual workstations. This includes the workstations in the field, home offices and satellite facilities. The data on theses PCS and workstations may contain important projects, critical documents, and irreplaceable creative works. Sometimes, even workstations in the home office or headerquarters may be overlooked, despite being tied directly into the corporate network.
Ensuring that you have backups for both the server and the workstations is one step to ensuring business continuity. Our new backup product allows for backups of the servers and the workstations. The backups can be stored locally on an in house backup server or backed up directly to the cloud, otherwise known as a disk-to-disk-to-cloud backup solution. This ensures that even if your local backup system fails, you will have another set of copies of backups stored in the cloud that you can easily deploy. This leads us directly into the next feature that is required for business continuity.
Ability to create backups locally as well as to the cloud
Until rather recently, in the last few years, the main option for backups were to do it all locally or on-premises. The backups were usually stored on a disk or even an additional tape drive. Larger businesses may have had another tier that sent backups off site for achriving. Research conducted by technology research firm of Gartner Inc, shows that backups in an average data center only worked about 85% of the time. Remote offices were even worse at 75% of the time. Making matters worse, is that you do not know if you have a bad backup until you attempt to restore it. With the introduction of the cloud, the game has changed. You can now backup fast and secure to a hybrid cloud backup. What do I mean by hybrid cloud backup?
The hybrid cloud backup or disk-to-disk-to-cloud, allows you to maintain an initial disk backup, which is still down in house, but has an additional tier that stores the backup in the cloud. This tends to be the best of both worlds as the cloud tier is scalable, easy to manager and guarantees data restores properly. Restoring from the cloud is perfect for remote offices that aren’t near the local disk backup. The main benefit of being able to restore a backup from disk or tape, is the speed of the restore. Our new backup software addresses the speed issue by only restoring the changed blocks on a system, which increases the speed of the restoration dramatically. How does only backing up the files that have changed on a system speed up the restore process?
Ability to only backup files that have changed in a system
What determines the speed of a backup? One factor would be the speed of the connection between the device or devices being backed up and the backup device itself. Another factor would also be the speed of the I/O(Input/Output) determined by the quickness of the disk. However, the biggest factor of them all when addressing the speed of a backup is the amount of data being backed up. Now, when you first create a backup, there is little that you can do to change the size of the data volume except for compression. The intitial backup copies the entire data set. There isn’t any way around this. Once the full backup is in place, maintaining the backup up is done by sending over only the changes of files.
Our new software does things a bit differently. Instead of backing up the changes to the file, the software instead only sends over changes to the blocks. Blocks are much smaller than a typical file. To put this in perspective, say you have a word document that is 300 KB in size. You edit the file and change one word in the file. A typical backup system will see the file has been changed and resend that entire file over to the backup software. That essentially won’t change the size of the file. What our new software does is looks at the changed block, representing the one word and send that over to the backup. This may not sound like a lot, but say you have thousands of files and have to resend every file, every time it has been changed. The size of the data will add up very quickly. The sending over of updates to only blocks of data is called Deep deduplication. Deep deduplication allows for a great savings in disk, or if you’re backing up in the cloud, service costs. It also means your network isn’t bogged down by having to transport massive data sets. Also, these smaller data volumes allow for increase longevity to your local backup system as you’re taking maximum advantage of your space.
To summarize, our new backup software addresses the main issues when discussing business continuity. Having business continuity for any business is a competivite advantage that every serious business owner must consider. Having a disaster recovery solution in place that you can deploy in a matter of minutes, will go a long way to ensure that your business is running at optimum efficiency. We’re calling our new backup software(Insert name of backup software). You should head over to (Insert URL to backup software) purchase some business continuity insurance for your business
For more information, check it out at TurnkeyVault.com
Follow Us :Share :